Inspirational journeys
Follow the stories of academics and their research expeditions
Secure Offboarding at Scale: Chain of Custody, Data Wipe, and ITAD You Can Audit
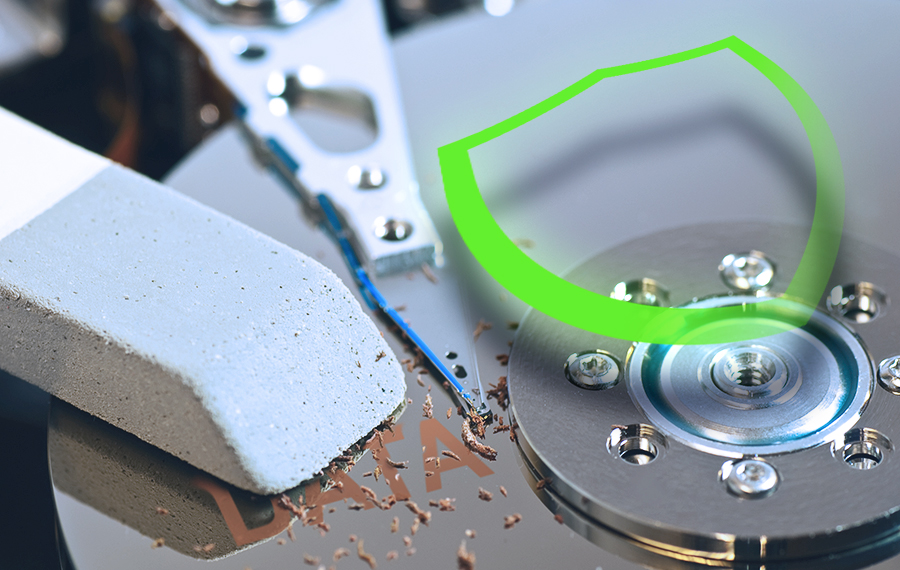
When hundreds of devices leave during offboarding each quarter, tracking each one is difficult. A missed laptop, active account, or incomplete data wipe can expose sensitive information and cause audit issues.
At scale, these problems multiply. Lost assets, missing certificates, or unverified IT asset disposition (ITAD) lead to compliance failures under GDPR, HIPAA, or SOC 2.
A secure offboarding process maintains a chain of custody, verifies data sanitization, and documents every step for audit. The goal is full control of data after devices and users exit the network.
Because offboarding starts with workforce changes, many organizations align HR systems and AI recruiting software with IT workflows to ensure exits, access revocation, and asset recovery stay synchronized
Building End-to-End Visibility with a Chain of Custody Framework
Every offboarding cycle creates risk. Devices hold personal, financial, and corporate data that remains valuable even after an employee leaves. When assets are transferred between users, storage, or vendors without proper documentation, visibility and compliance is compromised.
A chain of custody tracks each asset from collection to final disposition, recording who handled it, when, and under what conditions. This continuous record ensures accountability and provides evidence that can be presented during an audit or investigation.
A strong chain of custody matters most during storage, transit, and disposal. Each stage is a potential breach point. A secure framework limits access, maintains records, and verifies that every handoff follows approved IT policies and procedures for asset transfer.
Role-Based Offboarding Checklist
A role-based workflow maintains accountability and prevents security gaps:
Employee laptop agreement: Confirm that employees sign acknowledgment forms outlining asset ownership, return deadlines, and device condition requirements.
Identity disablement: Revoke user access from all systems before device retrieval.
Data sanitization: Apply approved wipe methods (per NIST 800-88) and record results.
Custody transfer: Document who receives each asset and confirm secure transit.
Verification and closure: Validate certificates, update asset inventory, and close records.
Each step creates traceable proof. When automated through an asset management platform, it becomes an auditable trail. A well-documented chain of custody protects organizations from unauthorized data exposure, lost equipment, and failed audits.
Data Sanitization Standards: How to Prove Information Is Gone for Good
Data sanitization is the process of permanently and irreversibly removing data from storage devices so that it cannot be recovered, even with forensic tools. It makes sure that no usable information remains on drives, disks, or memory components once assets are retired or redeployed.
According to the NIST 800-88 framework, data sanitization methods vary based on the device type, sensitivity of information, and whether the media will be reused or destroyed. Here are the three core sanitization levels: Clear, Purge, and Destroy.
Clear removes data using software-based overwriting methods.
Purge uses advanced techniques such as cryptographic erasure or degaussing.
Destroy physically dismantles or shreds the media, leaving no recoverable traces.
There are seven key sanitization methods used today: overwriting, degaussing, cryptographic erasure, physical destruction, secure erase, data masking, and SDelete.
Record-Keeping and Proof of Sanitization
Every sanitization event must create verifiable documentation, including:
Device ID and serial number
Sanitization method used
Date and responsible technician
Verification or destruction certificate
These records form the audit trail that regulators expect under frameworks like HIPAA, ISO 27001, and Sarbanes-Oxley.
Role of ITAD Partners in Strengthening Compliance and Audit Confidence
Improper disposal leaves organizations exposed to data recovery, theft, and non-compliance under frameworks like GDPR, HIPAA, and ISO 27001. Even a single unverified drive can compromise entire audit trails.
A certified ITAD partner closes that risk gap by providing three forms of protection: verifiable data sanitization, secure logistics, and complete reporting.
Here’s how ITAD partners strengthen compliance step by step:
Controlled Collection and Chain of Custody
Assets are picked up, sealed, and logged with serial numbers, timestamps, and custody records. This establishes a continuous trace from pickup to final processing.
Verified Data Sanitization or Destruction
ITAD vendors apply NIST 800-88 or DoD 5220.22-M methods such as degaussing, cryptographic erasure, or physical destruction. Each process generates a destruction certificate linked to the asset ID.
Environmental and Regulatory Compliance
Certified partners operate under global standards like R2v3 or e-Stewards, ensuring safe material handling and documentation that meets e-waste and privacy regulations.
Cross-Border Export Controls
For multinational teams, ITAD vendors manage export and re-import documentation to comply with the Basel Convention and local data-handling laws, avoiding shipment or retention violations.
Final Reporting and Audit Support
Each asset’s lifecycle ends with auditable proof or certificates of data destruction, recycling manifests, and chain-of-custody logs. These reports become part of your compliance record, ready for external or internal audits.
Secure offboarding isn’t complete when a device leaves the building. It’s completed when an ITAD partner proves, through data and documentation, that nothing valuable or vulnerable remains.
How to Balance Redeployment, Recycling, and Risk in IT Asset Offboarding
Secure offboarding doesn’t always mean destroying every asset. It’s about deciding which devices can be safely redeployed, which should be recycled, and which must be destroyed to protect data and compliance integrity.
Here’s how to get this balance right:
Redeployment for Cost and Sustainability Gains
Redeploying sanitized assets helps reduce hardware spending and supports sustainability targets. Properly wiped and verified devices can be reassigned to internal teams or secondary use cases without security risk.
However, redeployment only works when sanitization is documented and auditable. Without proof of data removal, reused assets can still fail compliance checks or expose residual information.
Recycling and Destruction for High-Risk Assets
If a device is obsolete, damaged, or contains sensitive or regulated data, secure destruction or certified recycling is the safer choice. These processes ensure no recoverable data remains and that materials are handled responsibly.
Partners certified under R2v3, e-Stewards, or WEEE standards assure that recycling and destruction meet data protection and environmental requirements.
Balancing Risk, Compliance, and Value
Each decision should be based on measurable criteria:
Data Sensitivity: Assess the type of data stored and potential exposure risk.
Device Condition: Confirm whether it’s reliable and economical to reuse.
Compliance Requirements: Verify regulations that restrict reuse or resale.
Residual Value: Consider cost savings or ESG gains from redeployment.
Assets that meet security and performance standards can be redeployed. Those that don’t should be recycled or destroyed with full certification.
Bottom Line
Secure offboarding isn’t achieved through one-time cleanup efforts but through consistent, repeatable controls that keep every asset and record accounted for.
As data volumes grow and hybrid work expands, offboarding will test how well organizations maintain visibility once assets leave users' hands. Building that reliability requires regular audits, vendor performance checks, and updated wipe verification policies.
0 Comments
Categories
- blog 968
Recent posts
Complete Guide To UG38 System
Sat, 18 Apr 2026

Why OLYMPUS88 is Redefining the Online Casino Experience
Fri, 17 Apr 2026



Leave a comment